What's new arround internet
| Src | Date (GMT) | Titre | Description | Tags | Stories | Notes |
| 2023-09-27 10:00:00 | Combiner la sécurité et la sécurité des OT pour une gestion des cyber-risques améliorée Combining IT and OT security for enhanced cyber risk management (lien direct) |
The content of this post is solely the responsibility of the author. AT&T does not adopt or endorse any of the views, positions, or information provided by the author in this article. Integrating IT and OT security for a comprehensive approach to cyber threats in the digital age. Historically, IT and OT have operated in separate worlds, each with distinct goals and protocols. IT, shaped by the digital age, has always emphasized the protection of data integrity and confidentiality. In this space, a data breach can lead to significant consequences, making it crucial to strengthen digital defenses. On the other hand, OT, a legacy of the Industrial Revolution, is all about ensuring machinery and processes run without interruptions. Any machine downtime can result in major production losses, making system availability and safety a top priority. This difference in focus has created a noticeable cultural gap. IT teams, often deep into data management, might not fully grasp the real-world impact of a stopped production line. Similarly, OT teams, closely connected to their machines, might not see the broader impact of a data breach. The technical challenges are just as significant. OT systems are made up of specialized equipment, many from a time before cybersecurity became a priority. When these older systems connect to modern IT networks, they can become weak points, open to today\'s cyber threats. This risk is even higher because many OT systems use unique protocols and hardware. These systems, once isolated, are now part of more extensive networks, making them accessible and vulnerable through different points in an organization\'s network. Additionally, common IT tasks, like updating software, can be more complex in OT. The equipment in OT often has specific requirements from their manufacturers. What\'s standard in IT can become a complicated task in OT because of the particular nature of its systems. Combining IT and OT is more than just a technical task; it\'s a significant change in how companies see and manage risks. From the physical risks during the Industrial Revolution, we\'ve moved to a time when online threats can have real-world effects. As companies become part of bigger digital networks and supply chains, the risks increase. The real challenge is how to unify IT and OT security strategies to manage cyber risks effectively. The imperative of unified security strategies According to a Deloitte study, a staggering 97% of organizations attribute many of their security challenges to their IT/OT convergence efforts. This suggests that the convergence of IT and OT presents significant challenges, highlighting the need for more effective security strategies that integrate both domains. Steps to integrate IT and OT security: Acknowledge the divide: The historical trajectories of IT and OT have been distinct. IT has emerged as a standardized facilitator of business processes, while OT has steadfastly managed tangible assets like production mechanisms and HVAC systems. Therefore, the first step towards a unified front is recognizing these inherent differences and fostering dialogues that bridge the understanding gap between IT and OT teams and leaders. Develop a unified security framework: Optimized architecture: Given the distinct design principles of OT, which traditionally prioritized isolated operations, it\'s crucial to devise an architecture that inherently safeguards each component. By doing so, any vulnerability in one part of the system won\'t jeopardize the overall network\'s stability and security. Regular vulnerability assessments: Both environments should be subjected to periodic assessments to identify and address potential weak links. Multi-factor authentication: For systems pivotal to critical inf | Data Breach Tool Vulnerability Threat Industrial | Deloitte | ★★ | |
| 2021-06-04 05:01:00 | Digital transformation explained (lien direct) |
This article was written by an independent guest author.
No matter what sector your organization does business in, you’ve probably heard the term digital transformation. In every industry, digital transformation is going to be critical to remain competitive and resilient.
But what does digital transformation mean? And how does cybersecurity fit in? Today’s organizations are facing an increasingly complex environment of securing everything attached to the network; applications, data, and endpoints.
What is digital transformation?
At its most basic definition, digital transformation (or DX) is the process of improving your business by leveraging the latest technologies and solutions.
Digital transformation harnesses third platform technologies - think cloud and data analytics, and acceleration technologies - think IoT and mobile apps to transform business operations.
The primary goals of digital transformation are to increase agility for customer responsiveness, flexibility to accommodate new ways of working, and scalability to help your business do more.
What’s driving digital transformation?
The main drivers of digital transformation are:
Skyrocketing data transmission speeds
Increased storage capacities
Expansion of mobile functionality
All these signs point to a rapid decrease of on-premises computing and storage.
With the cloud, the amount of time and resources spent on hardware maintenance and upkeep is drastically reduced because you no longer need to own, maintain, and upgrade these resources in your own data center.
Rebuffing the maintenance mindset, the preference for most IT departments is to spend more on innovation vs. the traditional “keep the lights on” tasks. However, because “turning the lights off” isn’t feasible, the bulk of IT budgets continue to be allocated to maintenance. A 2020 Deloitte Inisights report underscores the reality: the average IT department allocates over half its budget on maintenance but only 19 percent on innovation.
And according to a 2021 State of IT Spiceworks Ziff Davis study, updating outdated IT infrastructure is the number one factor driving IT budget increases — cited by 56% of organizations planning on growing IT spend.
Also driving cloud adoption is the need to address disaster recovery (DR). While DR has not been typically cost-effective for small to mid-sized businesses, many cloud vendors and providers offer DR solutions like DRaaS (Disaster Recovery as a Service) that address those challenges.
But perhaps the greatest driver of cloud adoption today is COVID-19. The pandemic’s disruption to the business landscape forced organizations to consider advanced technologies. The work from home or remote work model is here to stay, and the demand for software-as-a-service (SaaS) applications that allow teams to collaborate from anywhere is steadily increasing.
The main spheres of digital transformation
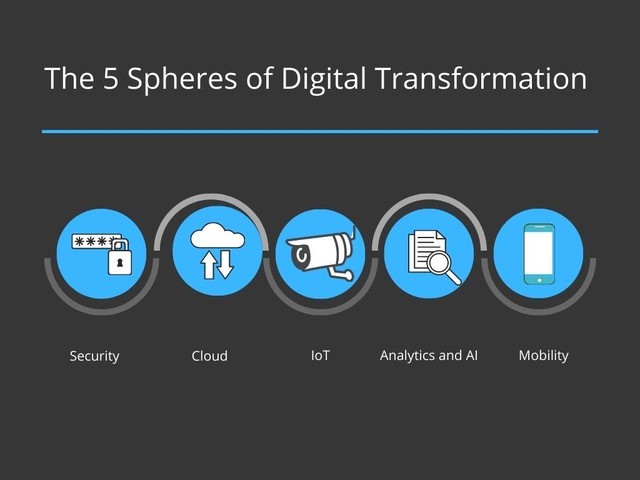 While one can argue that the components of digital transformation are numerous, we are highlighting five important spheres.
Security
As network access moves beyond the office perimeter to meet the demands of a remote workforce, robust security measures are required to maintain the confidentiality, integrity, and availability of corporate and customer data.
While one can argue that the components of digital transformation are numerous, we are highlighting five important spheres.
Security
As network access moves beyond the office perimeter to meet the demands of a remote workforce, robust security measures are required to maintain the confidentiality, integrity, and availability of corporate and customer data. |
Data Breach Threat | Deloitte | ||
| 2020-12-15 11:00:00 | Why application-layer encryption is essential for securing confidential data (lien direct) | This blog was written by an independent guest blogger. Your business is growing at a steady rate, and you have big plans for the future. Then, your organization gets hit by a cyberattack, causing a massive data breach. Suddenly, your company’s focus is shifted to sending out letters to angry customers informing them of the incident - which is required by law in most states - and devising strategies to deal with the backlash. This is an all too common scenario for many businesses, and the unfortunate truth is that most organizations fail to adopt the correct cybersecurity procedures until after an attack. The good news is that with a proactive approach to protecting your data, these kinds of nightmares can be avoided. New technology is constantly providing hackers new opportunities to commit cybercrimes. Most organizations have encrypted their data whether it’s stored on the cloud or in a server provided by their web host, but this isn’t enough. Even properly encrypted disc level encryption is vulnerable to security breaches. In this article, we will discuss the weaknesses found in disc level encryption and why it’s best to ensure your data is encrypted at the application layer. We’ll also discuss the importance of active involvement from a cybersecurity team in the beginning stages of application development, and why developers need to have a renewed focus on cybersecurity in a “security-as-code” culture. The importance of application-layer security Organizations all too often have a piecemeal, siloed approach to security. Increasingly competitive tech environments have pushed developers into building new products at a pace cybersecurity experts sometimes can’t keep up with. This is why it’s becoming more common for vulnerabilities to be detected only after an application launches or a data breach occurs. Application layer encryption reduces surface area and encrypts data at the application level. That means if one application is compromised, the entire system does not become at risk. To reduce attack surfaces, individual users and third parties should not have access to encrypted data or keys. This leaves would-be cybercriminals with only the customer-facing end of the application for finding vulnerabilities, and this can be easily protected and audited for security. Building AI and application-layer security into code Application layer security and building security into the coding itself requires that your DevOps and cybersecurity experts work closely together to form a DevSecOps dream team. Developers are increasingly working hand-in-hand with cybersecurity experts from the very beginning stages of software development to ensure a “security-as-code” culture is upheld. However, there are some very interesting developments in AI that present opportunities to streamline this process. In fact, 78% of data scientists agree that artificial intelligence will have the greatest impact on data protection for the decade. Here are four ways AI is transforming application layer security: 1. Misuse detection or application security breach detection Also referred to as signature-based detection, AI systems alert teams when familiar attack patterns are noticed. | Data Breach Vulnerability Threat | Deloitte | ||
| 2020-05-22 10:23:12 | Unemployment claimants suffer data breach (lien direct) | The social security numbers and home addresses of thousands of unemployment applicants inadvertently were exposed this week in three states that had contracted with Deloitte to build unemployment portals. In Ohio, Illinois and Colorado, thousands who applied for Pandemic Unemployment Assistance, or PUA, a type of unemployment newly available to the self-employed and gig workers, […] | Data Breach | Deloitte | ★★★★ | |
| 2019-01-07 06:05:00 | IDG Contributor Network: Managing identity and access management in uncertain times (lien direct) | If we remember one thing from 2018, it is that we are all victims now through one breach or another. Every day, we hear more news about another data breach affecting millions of users with significant financial and reputational consequences to its victims. With massive breaches like Equifax, Facebook, Deloitte, Quora and Yahoo, it is clear that breach notification services and multi-factor authentication (MFA) are not enough to prevent the next data breach headline from appearing in tomorrow's newspapers.Organizations have started thinking holistically, and rightly so, about risk and approaches to security using frameworks such as CARTA, Zero Trust, NIST SP 800 and IDSA. These frameworks offer progressive thinking and valuable approaches to modern identity strategy, but there is no one size fits all. These frameworks are akin to buying furniture from IKEA; assembly required, but with a lot more complexity and a lot more at stake. | Data Breach | Equifax Deloitte Yahoo |
1
We have: 5 articles.
We have: 5 articles.
To see everything:
Our RSS (filtrered)
